The Website That Turned a Security Firm Into a Security Brand
Armed escort. CCTV monitoring. VIP protection. Access control. Red Wolf Security had serious operational capability — they needed a digital presence that commanded the same authority.
Serious Security Capability Behind an Amateur Website
Red Wolf Security had the personnel, the licences, and the operational track record. Their website did not look like any of it.
Red Wolf Security is a Nigerian corporate security firm providing armed escort, CCTV surveillance installation and monitoring, VIP close protection, and access control solutions to commercial, corporate, and high-net-worth clients across Nigeria.
In Nigeria's corporate security sector, procurement decisions are trust-driven. A company's website is reviewed as a proxy for operational credibility — if the site looks amateur, the firm is perceived as amateur. Red Wolf's existing presence was failing them at the first evaluation point.
- Three distinct service categories (Armed Escort, CCTV, VIP Protection) were not clearly separated — corporate buyers could not immediately identify the specific capability they needed
- Licensing credentials and regulatory compliance — critical trust signals in the security sector — were entirely absent from the site
- No clear quote or engagement pathway — corporate procurement teams with urgent security requirements had no fast route to a conversation
- Visual design communicated no authority — the firm's years of operational experience and guard deployment scale were entirely invisible
Understanding the Corporate Security Buyer
The people who procure security services are evaluating risk on behalf of their organisation. We designed for that responsibility.
Buyer Persona Mapping
Three primary procurement profiles: Corporate Security Managers (responsible for site and personnel protection at multi-location businesses), HR and Facilities Directors (procuring access control and CCTV infrastructure), and Private Clients (HNW individuals requiring VIP close protection and residential security). Each carries different risk tolerance and decision timelines.
Trust Signal Audit
Security buyers evaluate in this order: regulatory compliance, operational scale, service specificity, and physical presence. The homepage was designed to surface licensing credentials, guard deployment numbers, and service category depth before a single marketing claim was made.
Service Clarity Problem
Armed escort, CCTV installation, and VIP protection attract fundamentally different buyers with different urgency levels and risk profiles. A single undifferentiated "Services" page was causing procurement confusion — buyers could not find their specific need quickly enough to stay on-site.
Competitor Landscape
Nigerian security firms typically present with generic, low-authority websites or no web presence at all. The gap between professional operational capability and digital presentation is significant across the sector. A well-executed corporate security website is a genuine competitive differentiator — not a luxury.
Lead with Authority. Then Show the Capability.
Security buyers do not want to be impressed — they want to feel safe making the decision. We designed for confidence, not persuasion.
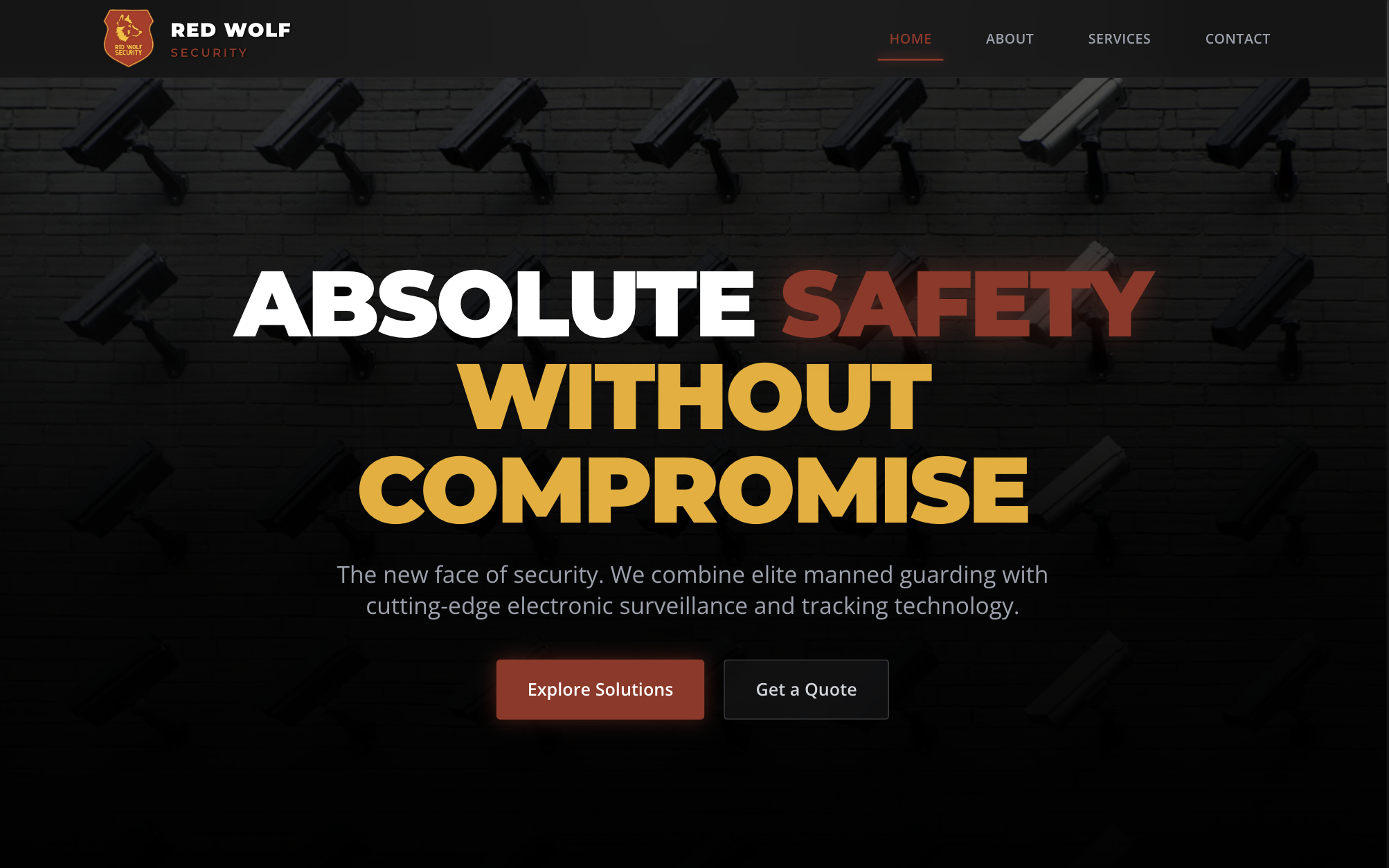
- Credential-first hero: Licensing status, years operating, and deployment scale placed in the hero — buyers encounter compliance proof before any service copy. Credentialling is the first filter in security procurement.
- Three-service architecture: Armed Escort / CCTV & Surveillance / VIP Protection — each category with its own dedicated section and page, targeting distinct procurement profiles with distinct urgency levels.
- Operational language: Copy written in the language of security operations — not marketing. "Rapid response," "asset protection," "threat assessment" — terms that resonate with professional buyers, not general audiences.
- 24/7 contact emphasis: Emergency contact number and "Request Security Assessment" CTA persist across all pages — security procurement is frequently time-sensitive and cannot wait for a business-hours response.
- Personnel visibility: Uniformed team photography humanises the brand — buyers are hiring people to protect their assets and people. Faces build the human trust that copy alone cannot achieve.
- Corporate visual identity: Deep red and near-black palette signals authority, urgency, and precision — the visual vocabulary of professional security across global markets.
Core Insight
"In security procurement, doubt equals disqualification. Every element on the Red Wolf site was designed to eliminate doubt — not to excite, but to satisfy."
Design for Authority: Command Presence in Every Element
A corporate security company's website should feel like a command centre — controlled, precise, and unambiguously professional.
Colour Palette
Credential Strip Hero
Licensed status, years operating, and guard deployment count displayed in the hero section — compliance proof appears before any service description. In security procurement, credentialling is the first and most important filter.
Three-Service Card System
Armed Escort, CCTV & Surveillance, and VIP Protection each presented as visually distinct category cards — buyers immediately identify their procurement need and navigate directly to relevant content without scanning undifferentiated service lists.
Personnel Photography
Uniformed guard imagery throughout — not stock photography, but visual representation of Red Wolf's operational reality. Security buyers need to see the team they are entrusting with asset and personnel protection.
24/7 Contact Persistence
Emergency contact number and security assessment CTA visible on every page. Security procurement is frequently time-sensitive — removing any friction between need and contact is a conversion imperative, not a design preference.
Command Typography
Heavy-weight, structured typeface communicates authority and decisiveness — the visual language of operational command. Nothing decorative. Nothing that reads as consumer. Security firms must look like security firms.
Dark-Mode Architecture
Near-black primary background with red accent — a colour system that communicates threat awareness, urgency, and professional authority. Intentionally differentiated from the light corporate aesthetics typical of the Nigerian business sector.
Three-service card system — clarity for distinct procurement profiles
Credential strip — licensing and deployment proof before claims
Homepage hero — authority established before a word is read
Built to the Same Standard Red Wolf Applies to Every Security Operation
Three service categories. 24/7 contact capability. Mobile-responsive across all devices. Zero tolerance for technical failure.
- Service category pages: Armed Escort, CCTV & Surveillance, and VIP Protection each have dedicated URLs — enabling service-specific SEO and direct procurement navigation per buyer type without content crossover.
- Security assessment form: Multi-field enquiry form capturing service type, location, number of personnel, and urgency level — pre-qualifies leads for Red Wolf's operational team from the first contact point.
-
Emergency contact
integration: Tap-to-call
phone number formatted as a
tel:link — one touch for time-sensitive security enquiries on any mobile device.
- Credential display component: Licensing status, registration number, and compliance certifications displayed in a structured trust strip — verifiable at a glance by any procurement officer conducting vendor due diligence.
- Personnel image gallery: WebP-optimised imagery of uniformed personnel — fast-loading across Nigeria's variable mobile network conditions without sacrificing visual authority or atmosphere.
- Google Maps integration: Office location with interactive map — physical address verification for procurement officers confirming vendor legitimacy and geographic reach.
Tech Stack
HTML5 · CSS3 (custom properties, flexbox, CSS Grid) · Vanilla JavaScript · Scroll-reveal animations · Google Maps API embed · Tap-to-call tel: integration · WebP optimised imagery · Schema.org SecurityService + LocalBusiness markup
Motion That Communicates Precision and Command
Deployment Counter
Personnel deployment count animates from zero to 200+ as users scroll into the statistics section — reinforcing operational scale through visual momentum rather than static copy. Numbers earned through operations carry authority that numbers written in a headline do not.
Service Card Reveals
The three service categories stagger into view with a controlled lift animation — deliberate, measured, professional. The sequence mirrors the systematic nature of security operations planning rather than the playful reveals common on consumer sites.
Navigation State
Active navigation item updates as users scroll through service sections — precise positional awareness maintained throughout. Security brands do not lose track of where they are or where they have been.
Scroll Reveals
Credential strips, service descriptions, and personnel imagery animate into view as the user scrolls — maintains engagement through a trust-dense corporate page without overwhelming the procurement reader with information all at once.
Animation Highlight — Deployment Counter
Watching 200+ count upward communicates earned scale — every number represents a guard at a client site, every hour of every day. Scale communicated through motion lands differently than scale stated in a bullet point.
Command Authority on Every Device
Nigeria's corporate security buyers evaluate vendors on mobile during site visits, in boardrooms, and in the field. The Red Wolf Security website performs identically on every device.
- Credential strip — Licensed Status / 200+ Guards / 24/7 Response — remains prominent and fully legible on the smallest mobile screens
- Three-service card grid collapses to clean single-column stacked layout — same procurement clarity, adapted for touch navigation
- Tap-to-call emergency number always visible and always one touch away — time-sensitive procurement cannot wait for desktop access
- Personnel photography maintains full visual authority on mobile — atmosphere and credibility preserved at every screen size


Found by Nigeria's Corporate Security Buyers
SEO Architecture
- Service pages create three independent keyword-ranking opportunities for high-commercial-intent security procurement searches
- Geographic targeting: "corporate security company Lagos Nigeria" + "armed escort services Nigeria"
- Schema.org SecurityService + LocalBusiness markup for Google Knowledge Panel eligibility
- Named personnel and licensing details signal Google E-E-A-T for security sector authority
Target Keywords
- "Armed escort services Nigeria" — Armed Escort service page
- "CCTV installation company Lagos" — CCTV & Surveillance service page
- "VIP protection Nigeria" — VIP Protection service page
- "corporate security company Nigeria" — Homepage and About page
A Digital Presence That Commands the Same Authority as Their Operational Capability
The Red Wolf Security website now communicates "serious professional security operation" before a service is clicked, before a quote is requested, before a meeting is booked.
What Red Wolf Said
★ ★ ★ ★ ★
Testimonial being collected from Red Wolf Security leadership — check back soon.
Ready for a website that commands this authority?
Do You Run a
Security Firm, Corporate Services,
or Professional
Services Organisation?
We build corporate websites that make serious buyers take you seriously — from security to infrastructure to professional services. Let's talk about what we would build for your organisation.